Did you know that according to a recent Cybersecurity Ventures report, cybercrime is expected to cost the world a staggering $10.5 trillion annually by 2025, outpacing the damage caused by natural disasters? In fact, as you read these lines, there’s likely another campaign of malicious code being deployed somewhere on the internet.
The need for software security has never been more urgent. For a great majority of companies, it’s only a matter of when, not if, they will be targeted.
In this digital era where everything is increasingly interconnected, software security is not just a luxury, but a necessity. It is paramount that businesses prioritize safety in their software development
process.
- Security vulnerabilities can leak sensitive data, disrupt operations, and could even bring businesses to a halt.
- Cyber attacks are growing in frequency and sophistication, and the consequences can be far-reaching, extending beyond monetary losses.
- Reputation erosion is one of the lesser talked about, yet incredibly damaging aftermaths of a successful cyber attack. Trust, once lost, can be extremely hard to regain.
Let’s delve deeper into the important role security plays in software development, and how incorporating security measures can save businesses from potential disasters.
1. Exploring Security Measures in Software Development
Ever wondered why security in software development is such a hot topic? Well, you’re not alone. In the age of unprecedented digital transformation, software security has become a paramount concern for individuals, businesses, and nations alike. It’s no longer just for the tech-savvy or IT professionals – it’s a matter that demands everyone’s attention.
Imagine a scenario where your valuable data, be it personal photos or sensitive company information, falls into the wrong hands due to weak software security. Sounds terrifying, right? Unfortunately, this is not a purely hypothetical situation. Such incidences have happened in the past, and they continue to haunt our cyber world. So, how can we prevent the repeat of such unfortunate scenarios?
The answer lies in how we approach software development. It’s crucial that we embed security into every step of the software development process. Rigorously secure development practices can mitigate cyber threats and react more effectively and efficiently when breaches occur. Intrigued? Let’s delve deeper into the importance of security in software development and discuss the best practices to ensure security in software development. Buckle up, you’re in for quite the ride!
2. Importance of Security in Software Development
Let’s dive right into an essential aspect of security in software development. Have you ever thought about how important it is? No software system exists in isolation. Interactions between systems, both within and outside of an organization, define today’s information landscape. This creates a need for an unrelenting emphasis on security in software development.
Why is it so crucial, you ask? The answer is simple. Security in software development is key to protecting data. Whether it’s personal information from customers or sensitive internal data, ensuring the security of this data is a top priority. Without these layers of defense, data breaches can exploit vulnerabilities, leading to reputational damage, financial loss, and legal consequences.
Besides safeguarding data, security in software development is essential for upholding user trust. How would you feel if the software that you put your faith in constantly faced breaches, and your data was continuously at risk? Certainly not very confident, right? This shows how security forms the foundation of the client-provider relationship.
In addition, integrating security in software development also makes economic sense. Would you like it if a software bug ended up costing you a small fortune to fix? Probably not. By identifying and mitigating security risks in the development stage, businesses can decrease the cost and effort of handling these problems down the line. It’s like that old saying “An ounce of prevention is worth a pound of cure.”
Finally, with changing regulations around the world, there’s never been a more critical time for organizations to prioritize security. Laws such as the General Data Protection Regulation (GDPR) in the European Union and the California Consumer Privacy Act (CCPA) in the United States, spell out stringent consequences for data breaches. So, security in software development helps ensure regulatory compliance, shielding businesses from fines and legal action.
So, as you can see, embracing security in software development is not just beneficial it’s imperative. In the next section, we will dive into some of the best practices that you should consider adopting to ensure security in the software development process.
3. Best Practices in Website Security
What do you think are the key factors to ensure a high degree of security for your website? Is it something you worry about each day? Truth be told, security should be a primary concern for every website owner. To maintain the trust of your site visitors and protect sensitive data, there are some best practices you should consider. Let’s take a closer look at these strategies.

3.1. SSL Certification
First and foremost, a Secure Sockets Layer, or SSL Certificate, is crucial. This adds an additional layer of security between your server and the user’s browser, securing data being transmitted, such as credit card information or login credentials. Websites with SSL are also perceived to be more trustworthy by search engines!
3.2. Data Sanitization
Don’t you think it’s paramount to protect your website from potential data injection? You’re absolutely right. Data sanitization, which refers to cleaning and examining input data before it gets processed, is a key security practice. This can help curtail SQL injection attacks and cross-site scripting.
3.3. Password Protection and Two-factor Authentication
You’ve probably come across the term two-factor authentication (2FA), haven’t you? It’s a technique that provides an extra layer of security by requiring users to provide two different authentication factors. By pairing this with password-protection measures (like encouraging strong, unique passwords and storing hashed passwords), you can dramatically amplify your website’s defense.
3.4. Regular Updates
Would you leave your front door unlocked and wide open? Unlikely, right? Likewise, failing to apply updates promptly is like leaving the doors of your website wide open to assailants. Regular updates, including those to the website’s platform, software, and plugins help protect the website from newly identified vulnerabilities.
3.5. Firewalls and Scanners
Your digital fortress deserves an unbreachable barrier, doesn’t it? Consider implementing web application firewalls to block suspicious traffic even before it reaches your site. Regularly using security scanners can also help detect malware, SQL injection attempts, or other vulnerabilities, proving them to be vital components of website security.
In conclusion, website security isn’t something you can achieve overnight. It’s a continuous effort, requiring regular monitoring and updating in response to new threats. But by following these best practices, you can make significant strides in safeguarding your site and fostering a trustful environment for your users.
4. Best Practices in Mobile App Security
As the digital landscape continues to evolve, so too does the need for robust security measures in mobile applications. But how, you might be wondering, does one ensure the security of a mobile application? Allow me to illuminate you to the primary environment where these best practices are applied.
You may not be surprised to learn that the most critical part of mobile application security begins in the early stages of the software development lifecycle.
Here, developers and security teams can many issues by implementing secure coding practices and conducting regular security reviews. Do you see? Protection starts not from the final steps, but from the very genesis of app creation.
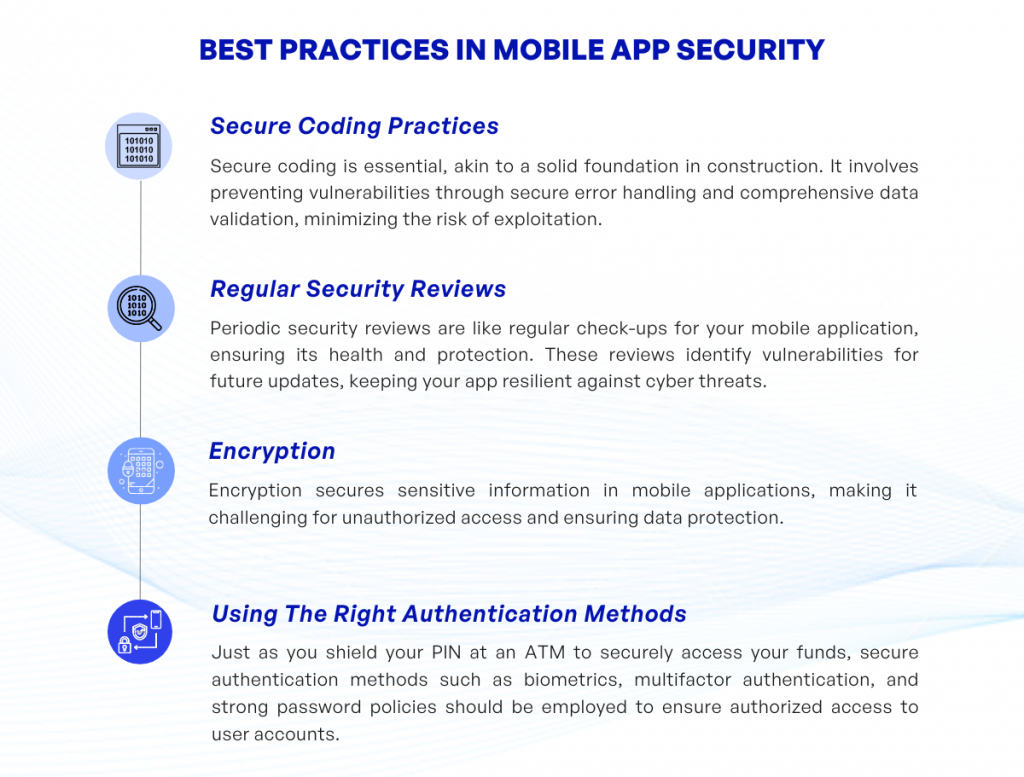
4.1. Secure Coding Practices
Secure coding is to the digital world as a solid foundation is to a building. Would you construct a skyscraper without first ensuring the groundwork is sound? A strong coding practice involves understanding how to prevent vulnerabilities, such as handling errors securely and validating all sorts of input data. If done correctly, it will ultimately minimize the risk of exploitation.
What’s the difference, you ask, between regular and secure coding? I’m glad you expressed that inquiry. It lies primarily in the anticipation of possible security flaws. While coding typically focuses on functionality and efficiency, secure coding places a significant emphasis on considering potential security vulnerabilities.
4.2. Regular Security Reviews
Think of these as a regular check-up for your mobile application. Just as your own health can benefit from regular screenings, so can your mobile application through periodic security reviews. These reviews identify the vulnerabilities in an app and mark them for fixes in future updates. By doing so continuously, it keeps your app healthy and away from being an easy target for cyber threats.
4.3. Encryption
Let’s illustrate encryption as a coded letter that only you and your best friend can decipher. In the world of mobile applications, all sensitive information should be encrypted before it is stored or transmitted. This makes it far more challenging for unauthorized users to access and misuse this information. So, you could say that encryption is the guarding knight of your app’s castle holding the secure key.
4.4. Using The Right Authentication Methods
Have you ever shielded your PIN while withdrawing cash from an ATM? It’s a simple way you authenticate yourself to take the money from your account securely. Similarly, secure authentication features like biometrics, multifactor authentication, and strong password policies should be used to ensure that the only person accessing an account is the person meant to be doing so.
Remember, following these best practices will equip your mobile application to fend off the ever-growing legion of cyber threats. Ultimately, the goal is not just to create an app that functions well, but to create one that can keep its users? information secure in all circumstances.
5. Security Checking Tools
If you’re thinking about software security, then you must not forget about security checking tools. Many might ask, what are these tools exactly? Security checking tools are essentially software applications that are designed to automatically spot security vulnerabilities, often making the programming environment safer and easier to manage. Quite a handy toolset, wouldn’t you agree?
But hold on a second. It’s not just that these tools are useful – they’re almost indispensable in today’s digital age. You see, the reality is that no code is perfect. You or one of your developers might make a tiny mistake, and this could potentially lead to a glaring security vulnerability. Here’s where security tools come in – they help you catch these errors before a hacker does.
So what types of security checking tools are there? Let’s delve into that a bit:
- Static application security testing (SAST): This type of tool analyzes your source code before it runs to identify potential vulnerabilities. It’s like a proofreader for your code!
- Dynamic application security testing (DAST): This tool, on the other hand, analyzes your application while it is running to find security flaws. It’s like a live security guard, keeping a close eye out for trouble.
- Software composition analysis (SCA): This tool checks the open-source and third-party components in your software for known vulnerabilities. A crucial tool, especially in today’s interconnected programming world where reuse and collaboration are common.
- Interactive application security testing (IAST): IAST tools are a combination of SAST and DAST, and they analyze both static code and running applications for vulnerabilities.
There’s no one-size-fits-all approach when it comes to security checking tools. It all really depends on the nature of your application, your team’s skills, and your particular security needs. Therefore, it’s crucial that you consider various factors before choosing your tools. Educate yourself, understand the pros and cons, and make an informed decision.
Remember, building secure software isn’t about avoiding failure it’s about planning for it. Security checking tools serve as your first line of defense, helping you plan for and mitigate potential security issues. So don’t let your guard down utilize security tools and stay one step ahead of potential threats. Sounds like a solid plan, doesn’t it?
6. Conclusion
There you have it, our detailed dive into the world of security in software development. We’ve explored critical tenets such as the importance of security measures and delved deeper into specific practices within the website and mobile app development. Remember, the effectiveness of your security approach depends on the balance you strike between preventative measures like SSL certification and reactive steps such as conducting regular security reviews. It’s all about staying vigilant!
Remember that in the fast-evolving digital realm, what works today may not be robust tomorrow. So, how do you stay a step ahead? By making security an integral part of your software development lifecycle. Embrace end-to-end security practices like secure coding, data sanitization, and strong authentication methods not only as an add-on but as an integral part of your development process.
So, are you ready to take your security practices up a notch? Of course, this comprehensive guide isn’t exhaustive. In the field of cyber security, there’s always more to learn, understand and implement. So be curious, continue learning, and most importantly, stay safe in the exciting yet challenging world of software development!
If you have any questions regarding security in product development, feel free to contact KVY TECH.