In this era where digital breaches are no longer a potential danger, but an inevitable hazard, Multi-Factor Authentication (MFA) emerges as a foundational pillar of security strategies – a silver bullet, if you will, against these cyber threats. Statistics published by the FBI confirm this assertion, revealing that the adoption of MFA could have prevented nearly 99% of data breaches in the past year alone. Astonishing, isn’t it?
According to the FBI, the implementation of Multi-Factor Authentication could have thwarted almost 99% of cyberattacks reported in the past year.
Imagine, if you will, a world where your online profiles, both personal and business, were not just protected by a single password, no matter how complicated or lengthy. Rather, gaining access requires multiple layers of ‘authentication factors’ working in tandem – an intricate dance of credentials that make unauthorized access exponentially more dificult. This is the magic that Multi-Factor Authentication works, yet so few understand.
1. What is Multi-Factor Authentication (MFA)?
Recognizing the rising tide of cyber threats and the utmost need to protect sensitive systems and data, security experts turned to a concept that builds upon a simple password: Multi-Factor Authentication (MFA) or Two-factor authentication (2FA). But, what exactly does this entail?
Simply put, MFA resides on an essential principle solidifying security by requiring multiple methods (or factors) to verify a user’s identity for a login or other transaction. In contrast to traditional authentication methods (where you would only present one piece of evidence your password), MFA demands two or more independent credentials: what the user knows (password), what the user has (security token), and what the user is (biometric verification).
This system is predicated on the notion that an unauthorized actor might be able to breach one defense mechanism, but it would be exponentially more dificult to intrude upon multiple barriers thus creating a robust defense against illegal access.
The logic and power behind MFA derive from its layers. Picture it this way: Your password alone is like a single door between a burglar and your precious belongings. However, imagine if the burglar came across a door (your password), then another door behind it (a unique code sent to your phone), and perhaps even another door behind that (a fingerprint scan). The additional layers would make it considerably tougher for them to get to your digital valuables.
Now that we understand what MFA is and why it offers an increased level of security, let’s delve deeper into the specific factors that make up Multi-Factor Authentication.
2. How Does Multi-Factor Authentication Work?
Gaining a deeper understanding of the intricacies involved in multi-factor authentication is indeed a need for the many of us relying heavily on this technology. Essentially, multi-factor authentication (MFA) is an interactive process, establishing a series of barricades between unauthorized users and your precious data, thereby adding extra layers to the security fortification.
Interested in knowing how multi-factor authentication actually works?
Picture this scenario – when you attempt to log into a site or system that uses MFA, you first enter your username and password (something you know), just like during a single-factor authentication process. This is your first line of defense, but we’re now diving into a stronger and more elaborate security strategy.
Aiming to significantly reduce the likelihood of a successful data breach, MFA steps in as your security reinforcement. Following the initial login stage, a second (and possibly third or more) factor gets introduced. This next stage could include things like:
- Something you have: A physical device, known as a hardware token, that generates a code that must be entered. Alternatively, a software token, or soft token, could be sent to a device you own such as your smartphone.
- Something you are: Here’s where biological traits come into play. Biometric data such as ?ngerprints, facial recognition, or retinal scans can confirm a user’s identity.
- Somewhere you are: Geographic location can likewise be a factor in authentication. For instance, you might receive a code through SMS or email if you’re logging in from a previously unknown location.
Only after successfully passing all these authentication stages, does the system finally grant you access. It’s a sequential process, each step increasing resistance against unwelcome, unlawful breaches.
Addressing a common question, one might wonder, “What happens if someone steals your hardware token or smartphone, potentially compromising ‘something you have”. Here’s where the strength of MFA truly shines. Even if an unauthorized person manages to acquire one factor, they still must bypass the other layers of security. In short, multi-factor authentication is not just a locking mechanism; it’s a powerful vault.
Understanding the process involved in multi-factor authentication can help you appreciate why it’s considered such an integral part of modern cybersecurity. Each factor involved in MFA serves a specific purpose, reinforcing the digital fortification of protection. Isn’t it worth keeping invaders at bay, safeguarding your digital treasure trove?
3. Types of Multi-Factor Authentication
In the digital landscape of today’s world, there exist numerous methods of performing multi-factor authentication, each providing different levels of security and convenience. Our varied digital identities necessitate this diversity, as different applications require different balances between the aforementioned factors. So, what are these methods, and how do they function?
Classically, multi-factor authentication has been divided into three primary categories: something the user knows (knowledge factors), something they have (possession factors), and something they are (inherence factors). Would you like to hear more? Let’s delve into it.
3.1. Knowledge Factors
Arguably the most common category among multi-factor authentication methods, knowledge factors involve something the user knows. A prime example would be the traditional password or Personal Identification Number (PIN) that you use for your numerous digital transactions. The strength of this category lies in its simplicity – simple to set up, and easy to use. However, with the rise of brute force attacks and phishing scams, the security of knowledge factors can sometimes be compromised.
Consider, for instance, how often we tend to forget our passwords and how predictable they sometimes become due to our preferences.
3.2. Possession Factors
Ever used a security token or received an SMS with a one-time password? If the answer is yes, you’ve interacted with possession factors, another category of multi-factor authentication. Possession factors work on the principle that only the rightful user should physically have access to a particular item. These could be security tokens, chip cards, or verification codes sent to your mobile device. The beauty of this category lies in its confirmation of the user’s physical presence, however, it can be inconvenient if the required device is misplaced.
3.3. Inherence Factors
Gaining popularity is biometric authentication, also known as inherence factors. This is all about identifying the unique biological and physical traits of the person accessing the system. It can involve ?ngerprint scans, facial recognition, even voice recognition, or retina scans. The benefits? They’re tough to fake and don’t require memory. On the other hand, concerns about privacy and the need for specialized devices might make this form of multi-factor authentication not suitable for every situation.
Ultimately, the right balance between these categories, considering both convenience and security, should dictate an organizations choice of multi-factor authentication methods. Bear in mind that each method has its strengths and its weaknesses; the choice should not be dictated by what’s currently ‘trending’ but rather by a clear, comprehensive understanding of each category. What works best for you? What would best serve your needs while minimizing potential risks?
4. Benefits of Multi-Factor Authentication

Multi-factor authentication (MFA), as a vital component of cybersecurity measures, brings numerous benefits, indeed. It acts as a fortress that throws an additional layer of security, thus, making defiling in?ltrations daunting even for the most seasoned hackers.
Yet, why is it essential for a business or an individual to implement Multi-Factor Authentication? And what are the tangible benefits of this security measure? Before we address these questions, let’s step back and consider? wouldn’t you want every possible tool at your disposal to ensure your data stays secure? With MFA, you unmask such a tool.
- Increased Security: This, being the most precipitated advantage of MFA, it’s important to note how monumentally it enhances security. By necessitating multiple pieces of evidence from a user before granting access, it actively deters unauthorized individuals. Even if a password gets compromised, and the additional authentication steps signify further hurdles for a potential intruder.
- Flexibility and Scalability: MFA can be easily adapted to meet a variety of needs. It can be applied on a small scale for individual use or scaled up to cover a vast corporate network. This adaptability allows it to seamlessly integrate into existing systems without requiring significant changes, making it a highly flexible, as well as robust solution.
- Compliance with Regulations: In certain industries, like finance and health, regulations require the use of MFA to protect sensitive data. By adopting MFA, organizations thereby fulfill regulatory requirements and avoid penalties.
- Improved Customer Trust: When customers understand that you’re taking additional steps to secure their data, it impacts their perception of your business positively. It’s not just that they feel safer, but it also fosters a sense of trust, a crucial aspect in any business relationship.
Could it be, perhaps, that Multi-Factor Authentication is the panacea to all cybersecurity threats? Definitely not. No system is infallible there will always be vulnerabilities and potential weaknesses, even within MFA. Yet, considering the increasing sophistication of cyber threats, adding extra layers of security seems, without a doubt, to be a wise course of action. Isn’t it better to be equipped with one more tool in your cybersecurity arsenal than to be caught off-guard?
So here we are, having rejected on the merits of MFA, it’s time to unbiasedly discuss its drawbacks. And yes, like every technology, it does have its share of them.
5. Disadvantages of Multi-Factor Authentication
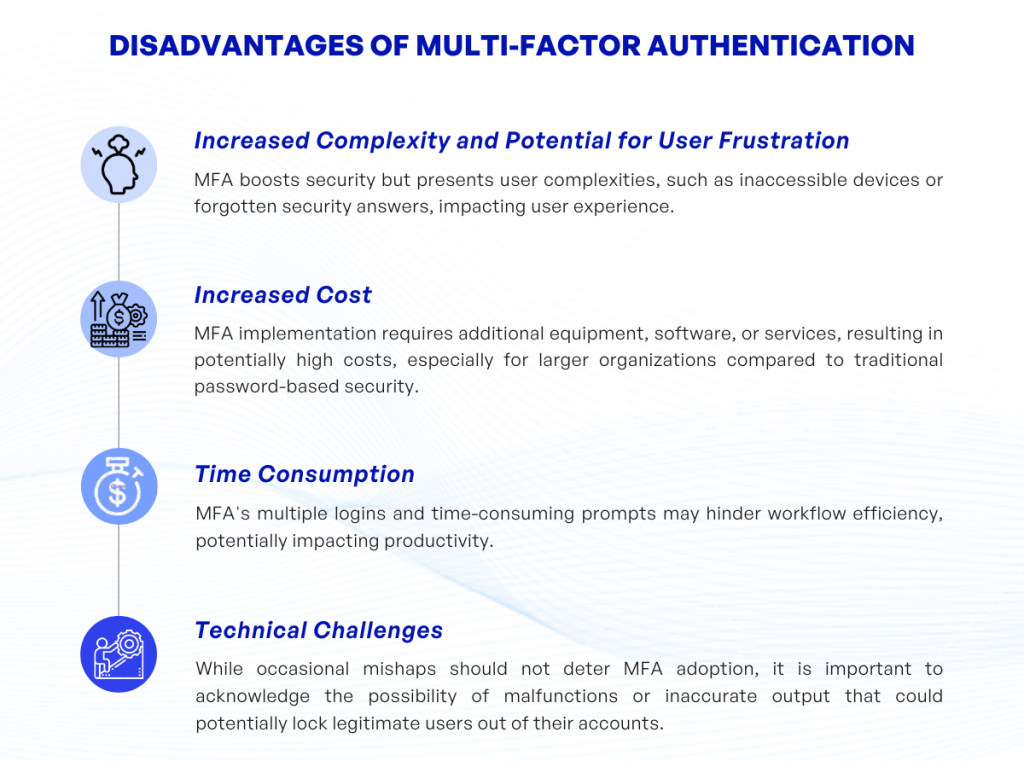
As commendable as the system of multi-factor authentication is (for its robustness in improving security), it does not come void of drawbacks. The adept utilization of MFA inevitably brings about certain complications and challenges, which can sometimes frustrate users and complicate the user experience. Therefore, it’s vital to consider these aspects when planning to implement such a method. Here are the most common disadvantages of multi-factor authentication.
- Increased Complexity and Potential for User Frustration: While MFA definitely increases security, it likewise adds an additional layer of complexity for the end-user. Imagine the inconvenience (and the moments of suspense), when you are unable to receive your email because your mobile device, functioning as your second factor, is not within reach. Or, how about those times when you forget the answer to a security question and are consequently barred from accessing a vital account? Doesn’t sound quite enthralling, does it?
- Increased Cost: Implementing a secure MFA system typically requires additional equipment, software, or services. These costs can accumulate (especially for larger organizations), making MFA a potentially expensive upgrade from traditional password-based security.
- Time Consumption: MFA requires more time for users to log in to various systems or apps, potentially causing delays in workflow. Imagine an employee, eager to begin their workday only to spend tiring minutes navigating through an MFA prompt. Could this be an inadvertent deterrent to productivity?
- Technical Challenges: Like other technological systems, multi-factor authentication can sometimes malfunction or provide inaccurate output, potentially locking legitimate users out of their accounts. While one shouldn’t let fear of such occasional mishaps prevent the adoption of MFA, it is a reality that deserves attention.
Understanding these disadvantages doesn’t negate the often necessary role MFA plays in securing digital identities and assets, rather, it illustrates that MFA (like any other protective measure) must be applied mindfully, considering both its strengths and weaknesses. After all, what good is a fortress if it locks out its rightful inhabitants?
6. Examples of Multi-Factor Authentication in Use
With the evolution of technology and increasing cybersecurity threats, Multi-Factor Authentication has been integrated seamlessly into various domains of our digital lives. It isn’t an exaggeration to say that you interact with MFA almost every day, often without realizing it. But what are some of these instances, you may ask? Let’s delve into a few examples of multi-factor authentication in use.
- Online Banking: Once you enter your username and password to access your bank account online, you’ve completed the first factor of authentication – the knowledge factor. The bank, however, doesn’t stop there. It usually sends a one-time password (OTP) to your registered mobile number, which you need to enter to gain access. This is the second factor, the possession factor. By leveraging these two categories of authentication factors, banks ensure that your online banking experience is secure.
- Social Media and Email Platforms: Ever noticed how you’re asked to enter a code sent to your mobile number or email when logging in from an unfamiliar device? That’s MFA at work, providing an extra layer of security to your digital presence.
- Mobile Payments: Mobile payment apps often require their users to authenticate transactions using biometrics, like fingerprints or facial recognition. This is intricately interwoven with the knowledge factor, like a password, to ensure the safeguarding of your transactions.
- Cloud Storage Services: Services like Google Drive and Dropbox often provide an option to set up two-factor authentication. With this, you would need your password and then a device-specific code, providing another layer of protection for your devices.
These examples, while not exhaustive, provide an insight into the omnipresence of multi-factor authentication in our everyday digital interactions. It’s worth rejecting on how it serves as an essential barrier, protecting our personal and professional data from unauthorized access.
7. Final thoughts
In the grand scheme of digital security, multi-factor authentication (MFA) undoubtedly stands as a stalwart sentinel, defending our sensitive data from would-be intruders. The beauty (or shall we say, the sophistication) of MFA lies in its layered approach, making illicit access significantly more challenging. Who knew combining something you know, something you have, and something you are could form such a robust shield?
Indeed, from the perspective of organizations be it multinational corporations, financial institutions, or burgeoning start-ups MFA has become not an option, but a necessity. This isn’t surprising, is it? After all, falling victim to a security breach is a nightmare no organization, irrespective of its size or stature, would want to entertain, let alone experience.
Furthermore, MFA comes packed with benefits. Increased security can never be downplayed in an era where cyber threats are as commonplace as the devices we use. Offering a high level of assurance, it adds an extra layer of protection, fortifying credentials against possible exposure. What’s more? Customer trust is enhanced, a significant achievement in this digital age where trust is, often, as valuable as the services or products the organization provides.
MFA may arguably not be as user-friendly and can potentially slow down system access, a trade- some organizations, particularly those where speed is earnestly required, might find inconvenient. Furthermore, remember that elevated security levels also mean increased costs a factor that could potentially deter small to medium-sized enterprises.
Multi-factor authentication, with its various types and processes, holds the fort while we traverse the digital landscape a terrain that, while incredibly useful and revolutionary, isn’t without its threats and hazards. It, therefore, becomes critical to employ such comprehensive protective measures in our cybersecurity strategy.
As we move forward in this digital era, the importance of multi-factor authentication will only continue to grow. Now, isn’t that something to think about as we navigate an ever-evolving digital landscape?
If you have any questions about multi-factor authentication, feel free to contact KVY TECH.